PDF] Power Consumption-based Detection of Sabotage Attacks in
Por um escritor misterioso
Descrição
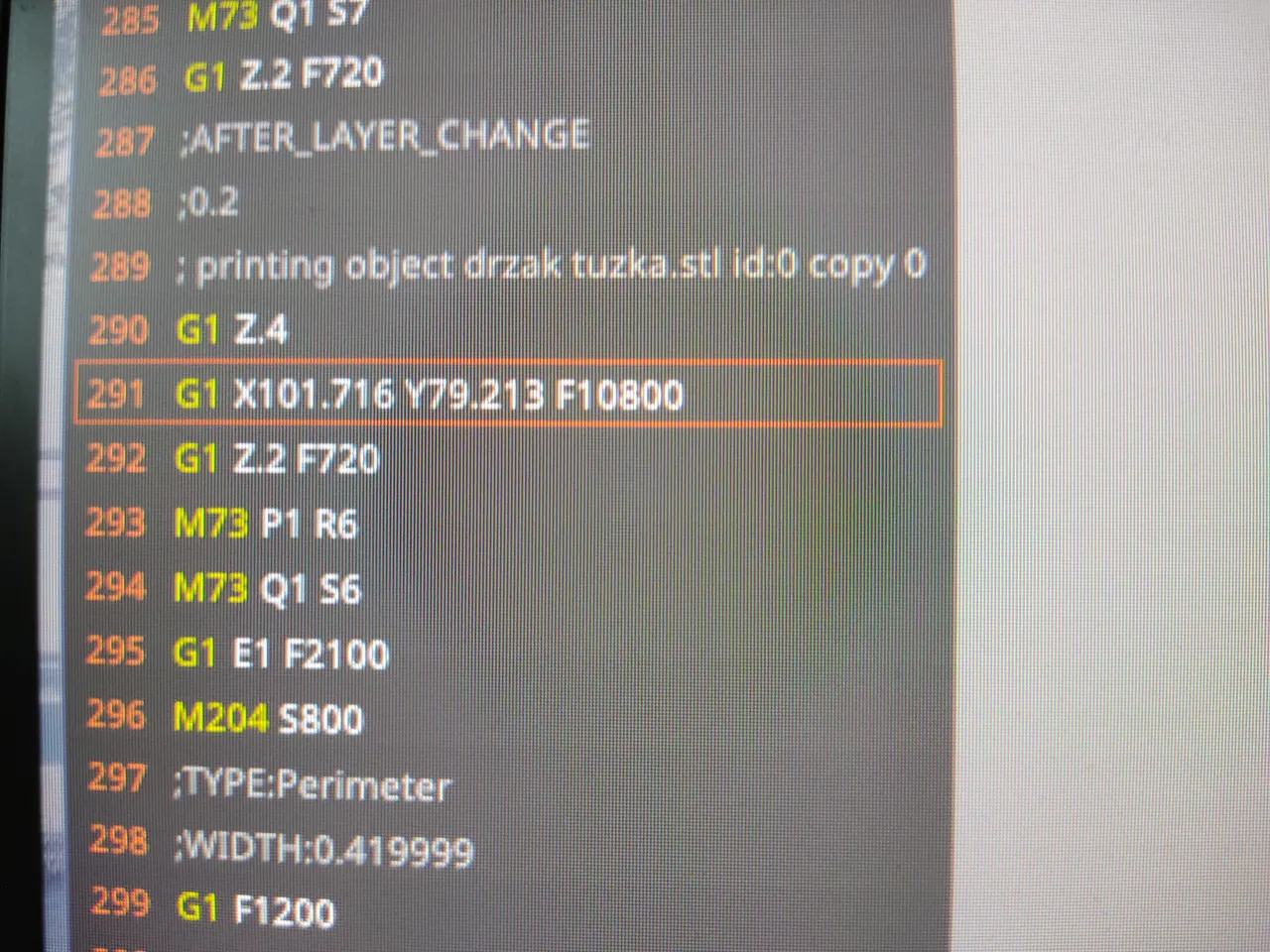
This work proposes a novel approach for detecting sabotage attacks in additive Manufacturing, based on continuous monitoring of the current delivered to all actuators during the manufacturing process and detection of deviations from a provable benign process. Additive Manufacturing (AM), a.k.a. 3D Printing, is increasingly used to manufacture functional parts of safety-critical systems. AM's dependence on computerization raises the concern that the AM process can be tampered with, and a part's mechanical properties sabotaged. This can lead to the destruction of a system employing the sabotaged part, causing loss of life, financial damage, and reputation loss. To address this threat, we propose a novel approach for detecting sabotage attacks. Our approach is based on continuous monitoring of the current delivered to all actuators during the manufacturing process and detection of deviations from a provable benign process. The proposed approach has numerous advantages: (i) it is non-invasive in a time-critical process, (ii) it can be retrofitted in legacy systems, and (iii) it is airgapped from the computerized components of the AM process, preventing simultaneous compromise. Evaluation on a desktop 3D Printer detects all attacks involving a modification of X or Y motor movement, with false positives at 0%.
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://media.springernature.com/m685/springer-static/image/art%3A10.1038%2Fs41598-022-12181-w/MediaObjects/41598_2022_12181_Fig1_HTML.png)
An energy-aware and Q-learning-based area coverage for oil pipeline monitoring systems using sensors and Internet of Things
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://d3i71xaburhd42.cloudfront.net/d81c8d2816032b4abc1798383f88d5a376d17a75/14-Figure10-1.png)
PDF] Power Consumption-based Detection of Sabotage Attacks in Additive Manufacturing
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://ars.els-cdn.com/content/image/1-s2.0-S2405844023043645-gr7.jpg)
A systematic literature review for APT detection and Effective Cyber Situational Awareness (ECSA) conceptual model - ScienceDirect
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://www.ironnet.com/hubfs/Attacks%20on%20the%20Power%20Grid%20v2%20-%20infographic.png)
Cyber Attacks on the Power Grid
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://ietresearch.onlinelibrary.wiley.com/cms/asset/3da0c48b-c5ee-42dd-9bf0-975b59c48459/gtd212766-fig-0002-m.jpg)
A novel cyber‐attack modelling and detection in overcurrent protection relays based on wavelet signature analysis - Yousefi kia - 2023 - IET Generation, Transmission & Distribution - Wiley Online Library
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://image.slidesharecdn.com/lightsecforutilitiesandcriticalinfrastructurewhitepaper-160912065753/85/light-sec-for-utilities-and-critical-infrastructure-white-paper-1-320.jpg?cb=1670704168)
Light sec for utilities and critical infrastructure white paper
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://www.frontiersin.org/files/Articles/884192/frai-05-884192-HTML-r1/image_m/frai-05-884192-g001.jpg)
Frontiers Recommendations for ethical and responsible use of artificial intelligence in digital agriculture
Full article: Black start: the risk of grid failure from a cyber attack and the policies needed to prepare for it
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://ars.els-cdn.com/content/image/1-s2.0-S0278612522000632-gr5.jpg)
Physics-based detection of cyber-attacks in manufacturing systems: A machining case study - ScienceDirect
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://www.researchgate.net/publication/334407323/figure/fig2/AS:779804659970048@1562931327031/Power-Consumption-Signature-Generation_Q320.jpg)
PDF) Detecting Sabotage Attacks in Additive Manufacturing Using Actuator Power Signatures
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://ars.els-cdn.com/content/image/1-s2.0-S0278612522000632-gr6.jpg)
Physics-based detection of cyber-attacks in manufacturing systems: A machining case study - ScienceDirect
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://imgv2-1-f.scribdassets.com/img/document/21008921/298x396/355aedba87/1642624460?v=1)
Simple Sabotage Field Manual, PDF, Project Gutenberg
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://d3i71xaburhd42.cloudfront.net/d81c8d2816032b4abc1798383f88d5a376d17a75/15-Figure11-1.png)
PDF] Power Consumption-based Detection of Sabotage Attacks in Additive Manufacturing
![PDF] Power Consumption-based Detection of Sabotage Attacks in](https://d2908q01vomqb2.cloudfront.net/f1f836cb4ea6efb2a0b1b99f41ad8b103eff4b59/2022/07/14/image015.png)
How Sophos trains a powerful, lightweight PDF malware detector at ultra scale with SageMaker
de
por adulto (o preço varia de acordo com o tamanho do grupo)