Cmd Hijack - a command/argument confusion with path traversal in cmd.exe
Por um escritor misterioso
Descrição
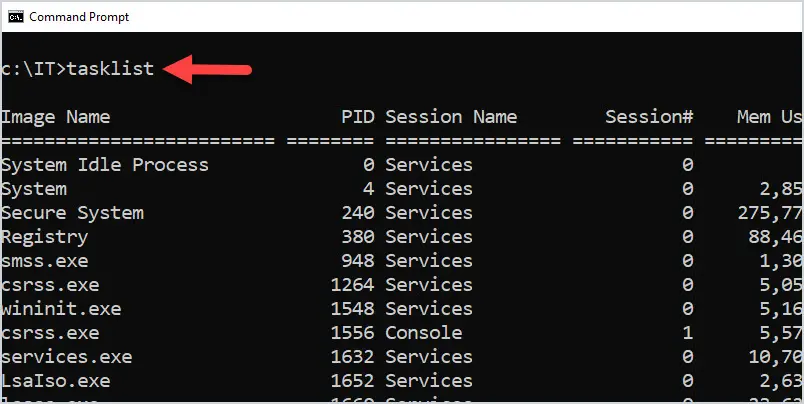
This one is about an interesting behavior 🤭 I identified in cmd.exe in result of many weeks of intermittent (private time, every now and then) research in pursuit of some new OS Command Injection attack vectors.
So I was mostly trying to:
* find an encoding missmatch between some command check/sanitization code and the rest of the program, allowing to smuggle the ASCII version of the existing command separators in the second byte of a wide char (for a moment I believed I had it in the StripQ

Cmd Hijack - a command/argument confusion with path traversal in cmd.exe : r/netsec
Dissecting Macro Malware - Use CMD Path Traversal Hijacking Technique (PING!) - Malware Analysis - Malware Analysis, News and Indicators
Swedish Windows Security User Group » Microsoft security intelligence
Process Injection Part 1: The Theory - Secarma: Penetration Testing and Cybersecurity Company

0xdf hacks stuff CTF solutions, malware analysis, home lab development

Command And Conquer. Exploring the Command Promp-Part2, by Glen Sauve

Indirect Command Execution – Penetration Testing Lab

0xdf hacks stuff CTF solutions, malware analysis, home lab development

Indirect Command Execution – Penetration Testing Lab
running a cmd within powershell - Microsoft Q&A

Hamza Rabbani (@hamzarabbani00) / X

de
por adulto (o preço varia de acordo com o tamanho do grupo)
:max_bytes(150000):strip_icc()/psexec-ipconfig-command-5c6ef8dc46e0fb0001b68174.png)
.jpg.transform/9col/image.jpg)


