Pawn Storm Abuses OAuth In Social Engineering Attacks
Por um escritor misterioso
Descrição
This blog post discusses how Pawn Storm abused Open Authentication (OAuth) in advanced social engineering schemes. High profile users of free webmail were targeted by campaigns between 2015 and 2016.

Pawn Storm behind cyber-attacks on organisations conducting Winter Olympics
MITRE ATTCK Technique Spearphishing Link SECURITM
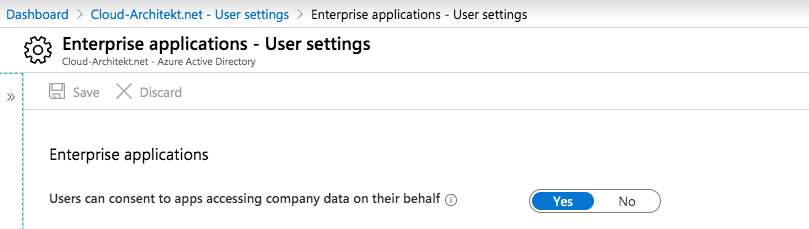
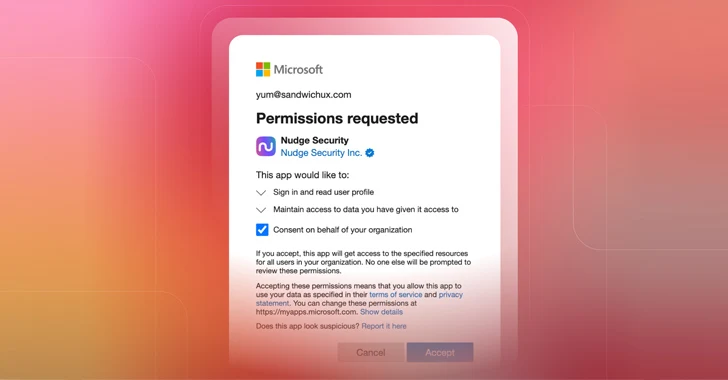
Detection and Mitigation of Illicit Consent Grant Attacks in Azure AD - Thomas Naunheim
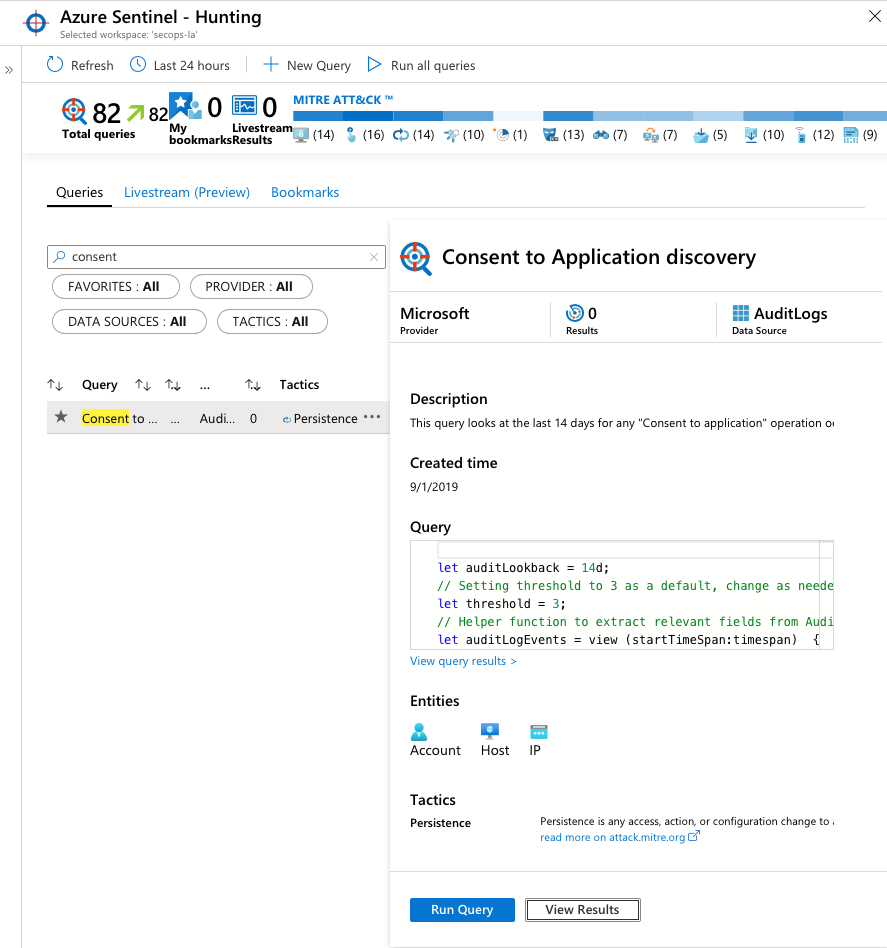
Detection and Mitigation of Illicit Consent Grant Attacks in Azure AD - Thomas Naunheim
How to Protect Against Social Engineering Attacks?
OAuth, Breaking Cybersecurity News

Hackers Abusing OAuth Token to Take Over Millions of Accounts

Microsoft Warns of Hackers Exploiting OAuth for Cryptocurrency Mining and Phishing

STIDIA
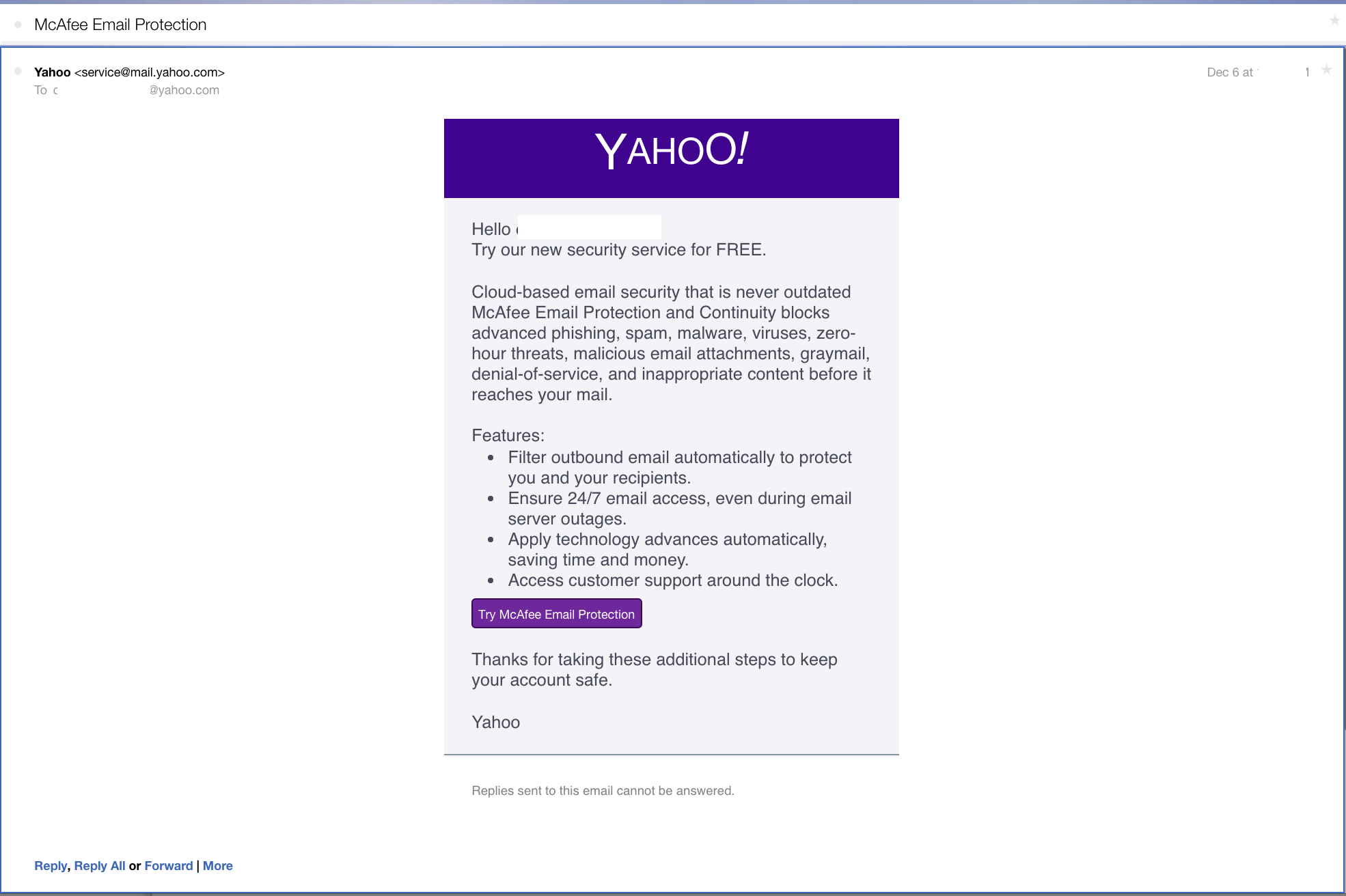
Pawn Storm Abuses OAuth In Social Engineering Attacks
What are Social Engineering Attacks? Types of Attacks in 2023

What Are Social Engineering Attacks and How to Prevent Them - SEON
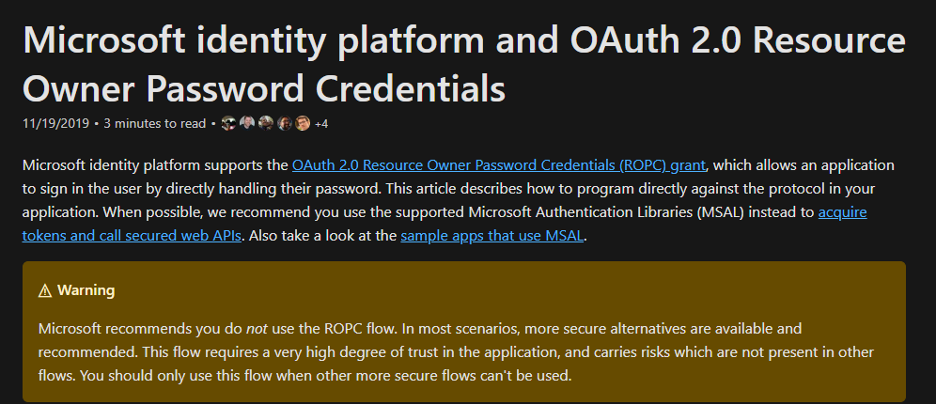
TrustedSec Practical OAuth Abuse for Offensive Operations – Part 1

APT28 relies on PowerPoint Mouseover to deliver Graphite malware

Ontological Model of a Social Engineering Attack [in accordance with 10].
de
por adulto (o preço varia de acordo com o tamanho do grupo)