Malware analysis Malicious activity
Por um escritor misterioso
Descrição

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog

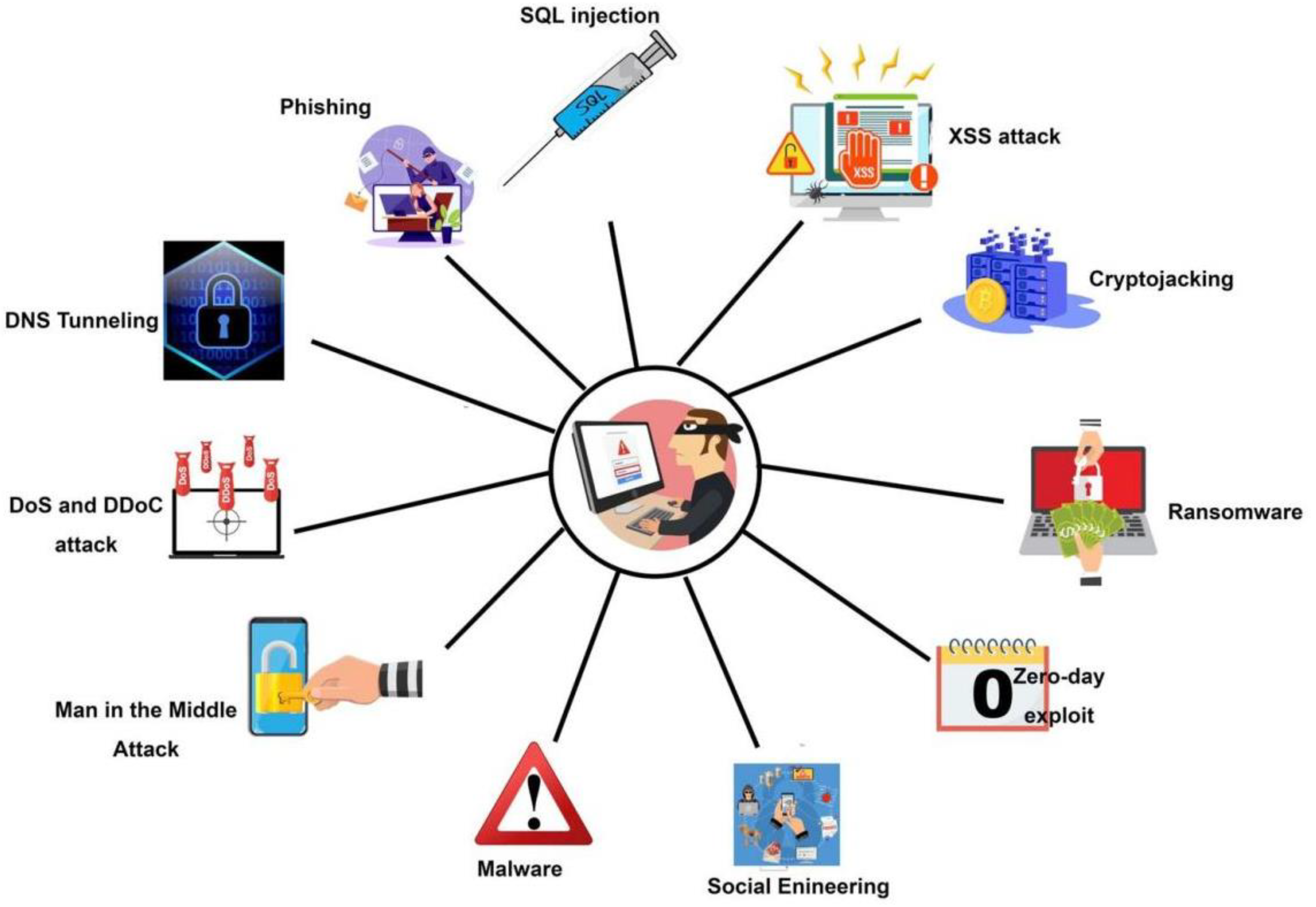
Malware Analysis: Protecting Your Network from Cyber Attacks

Malware Analysis Benefits Incident Response

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

Robust Malware Detection Models: Learning From Adversarial Attacks and Defenses - Forensic Focus

Remediation and Malware Detection Overview

Static malware analysis workflow.
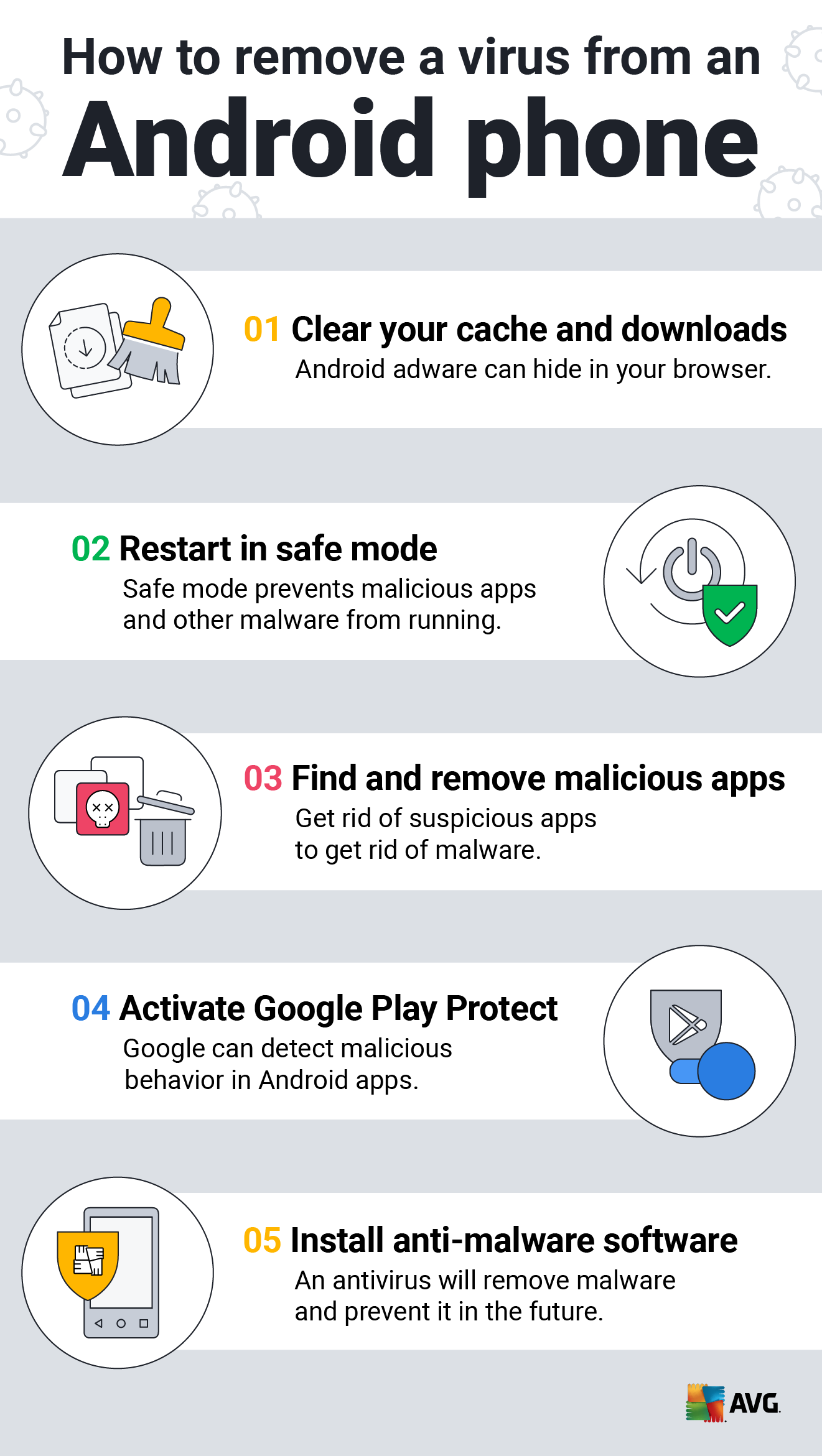
How to Clean an Android or iPhone from Viruses for Free
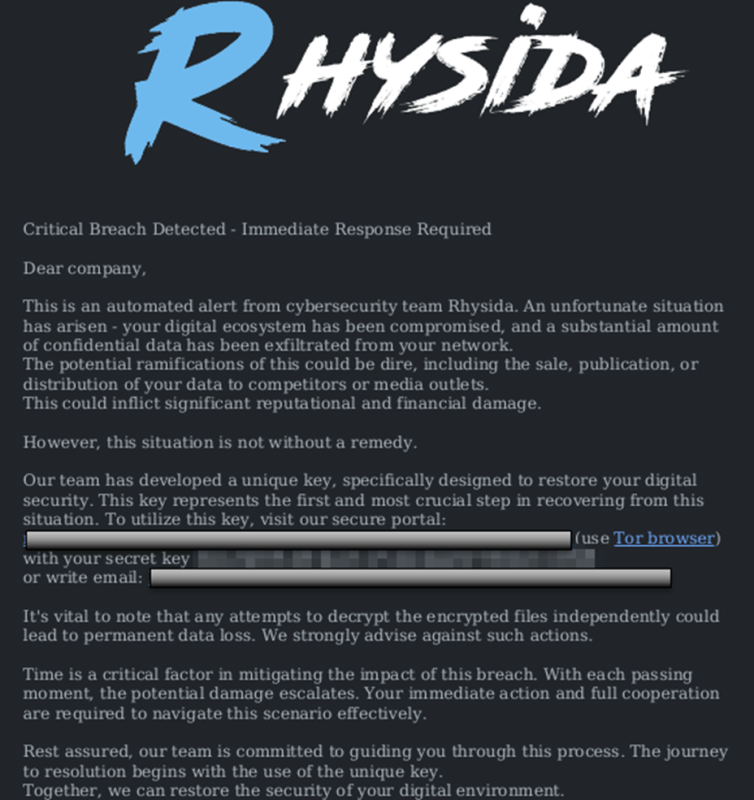
StopRansomware: Rhysida Ransomware
Symmetry, Free Full-Text

What Is Malware Analysis? Definition, Types, Stages, and Best Practices - Spiceworks

Malware Analysis: Steps & Examples - CrowdStrike

Malware analysis file Malicious activity

FBI, CISA, MS-ISAC release cybersecurity advisory on emerging Rhysida ransomware targeting critical sectors - Industrial Cyber
TryHackMe Hacktivities
de
por adulto (o preço varia de acordo com o tamanho do grupo)