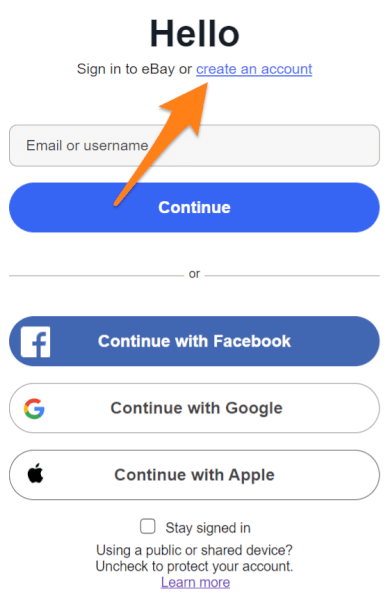
Cyber Criminals Phishing for Account Access
Por um escritor misterioso
Descrição

Cybercriminals Increasingly Using EvilProxy Phishing Kit to Target
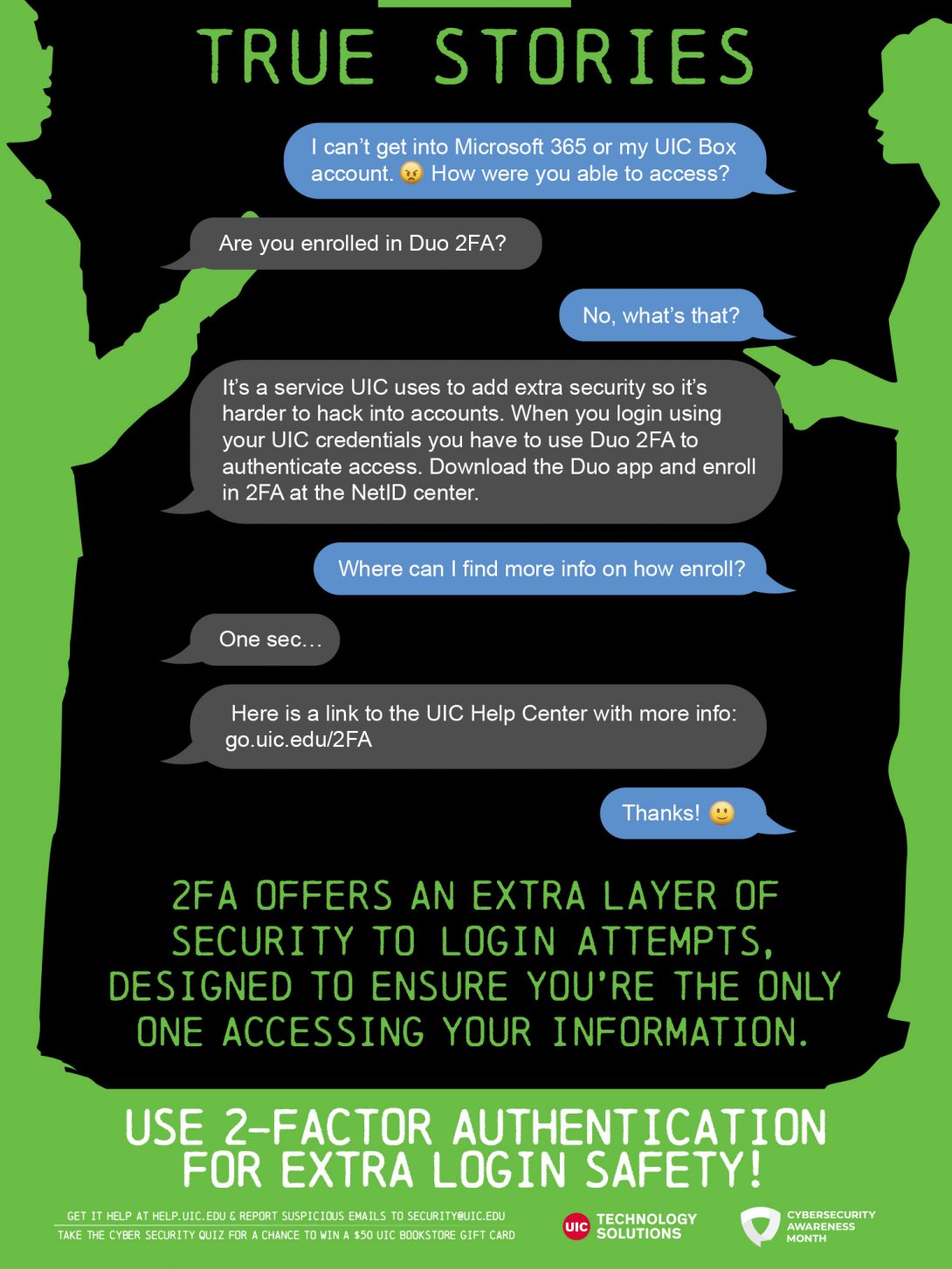
True Stories: Use 2-Factor Authentication for Extra Login Safety

Hacker Attack And Cyber Criminals Phishing Stealing Private

How does MFA prevent MiTM phishing attacks?

Cybercriminals are always looking for ways to get their hands on

The Latest Phishing Statistics (updated December 2023)
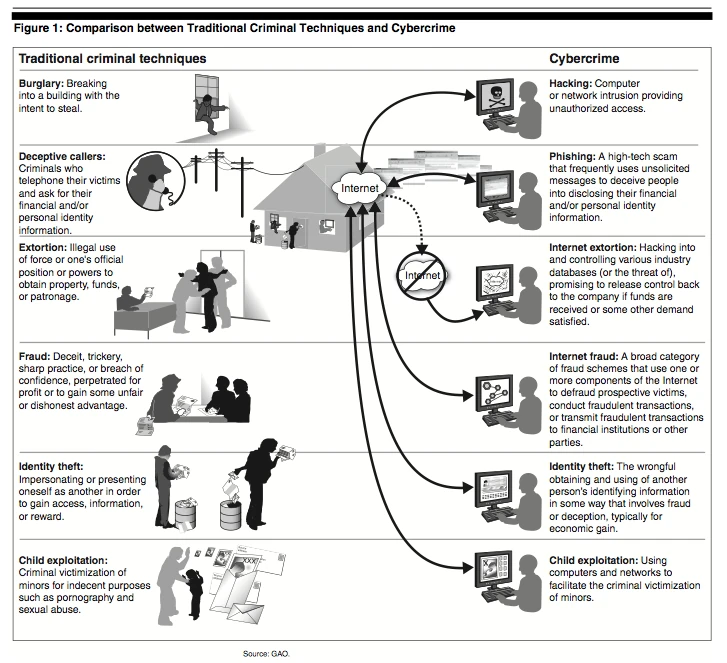
Cybercrime, The IT Law Wiki
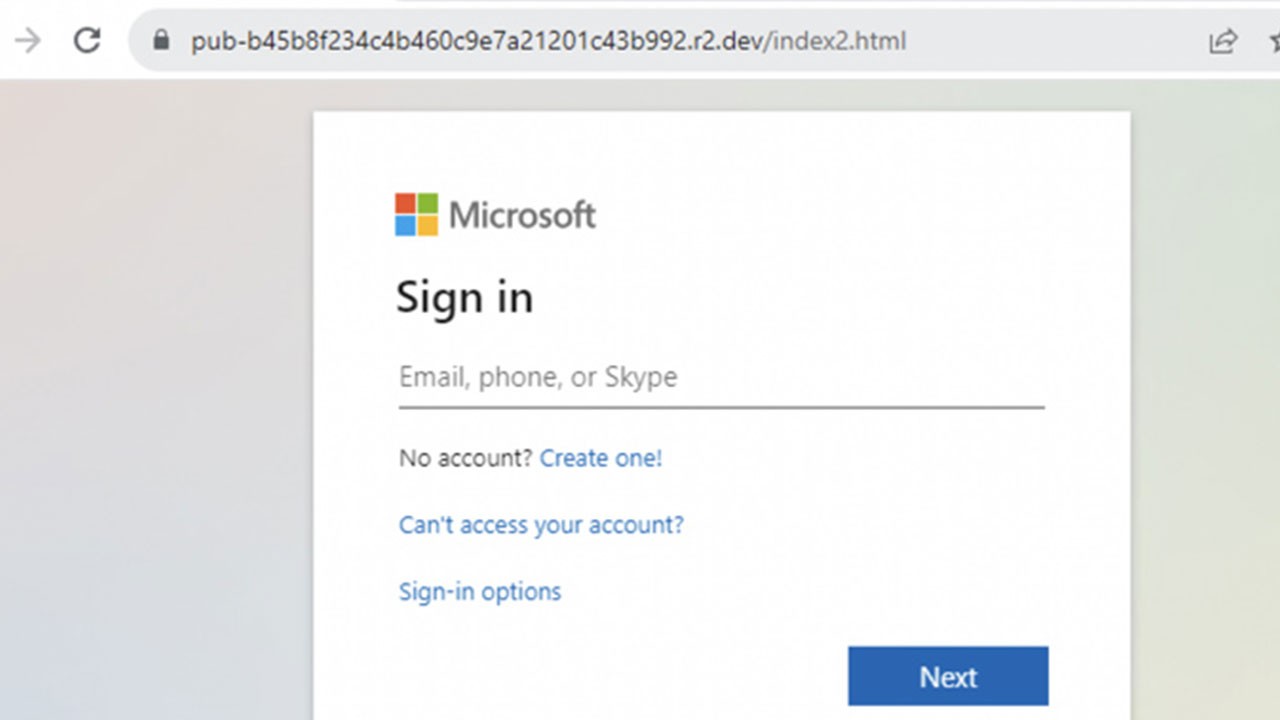
Cybercriminals Abusing Cloudflare R2 for Hosting Phishing Pages

Cyber Criminals Vector & Photo (Free Trial)

How Cybercriminals Use Social Engineering to Access Sensitive

LinkedIn being targeted by cyber criminals through phishing attacks
Sharpen Your Cyber Security Skills: Spoofing and Phishing

Hackers and cyber criminals engage in phishing, identity theft

Inside a Compromised Account: How Cybercriminals Use Them
de
por adulto (o preço varia de acordo com o tamanho do grupo)